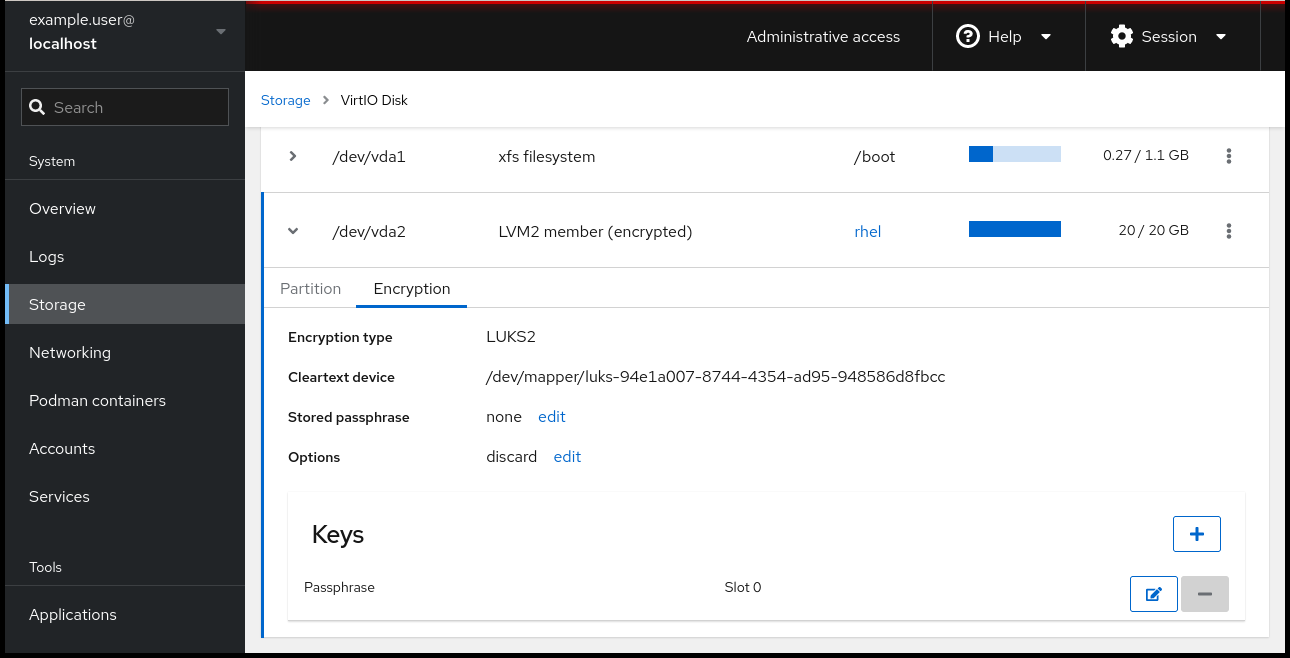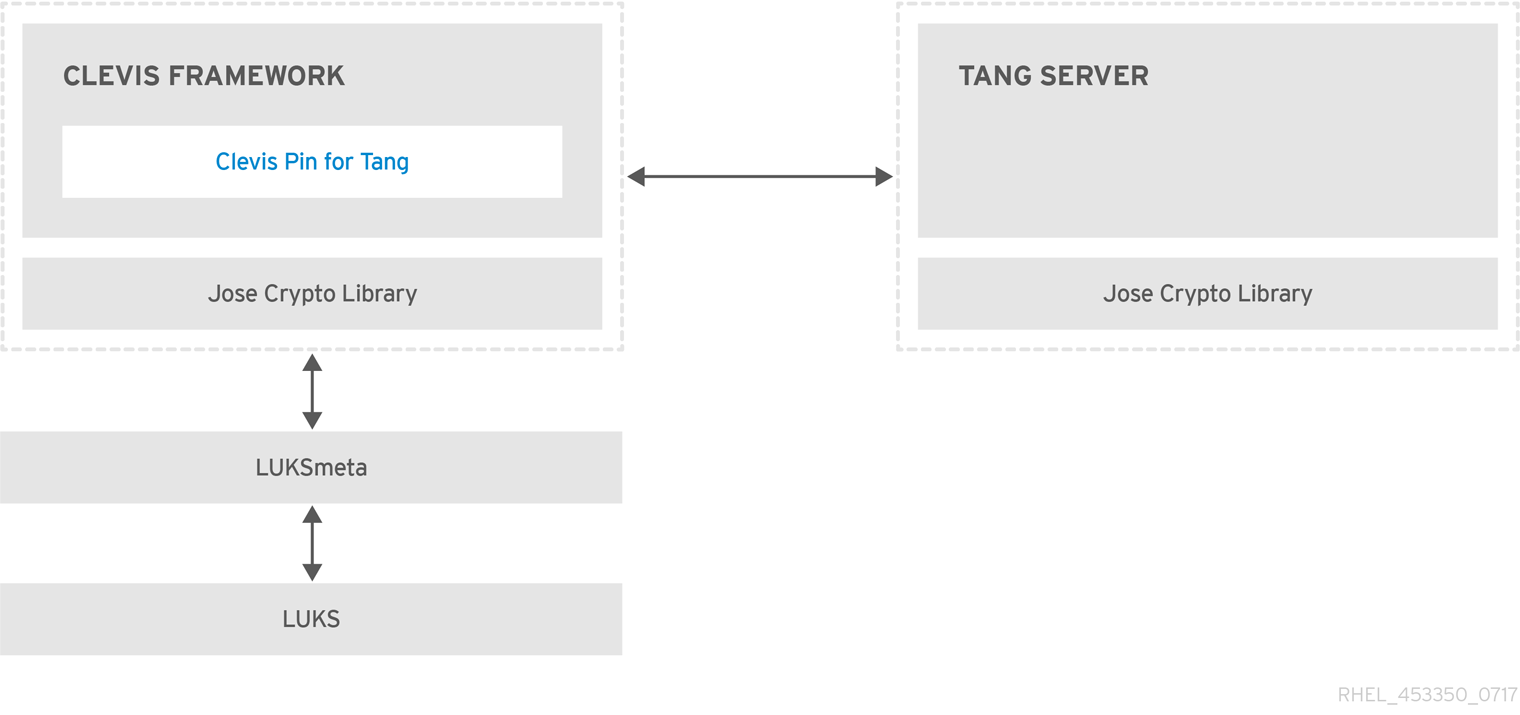
4.10. Configuring Automated Unlocking of Encrypted Volumes using Policy-Based Decryption Red Hat Enterprise Linux 7 | Red Hat Customer Portal
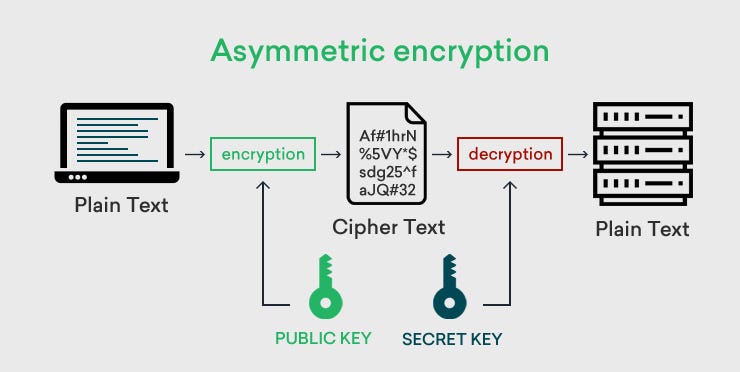
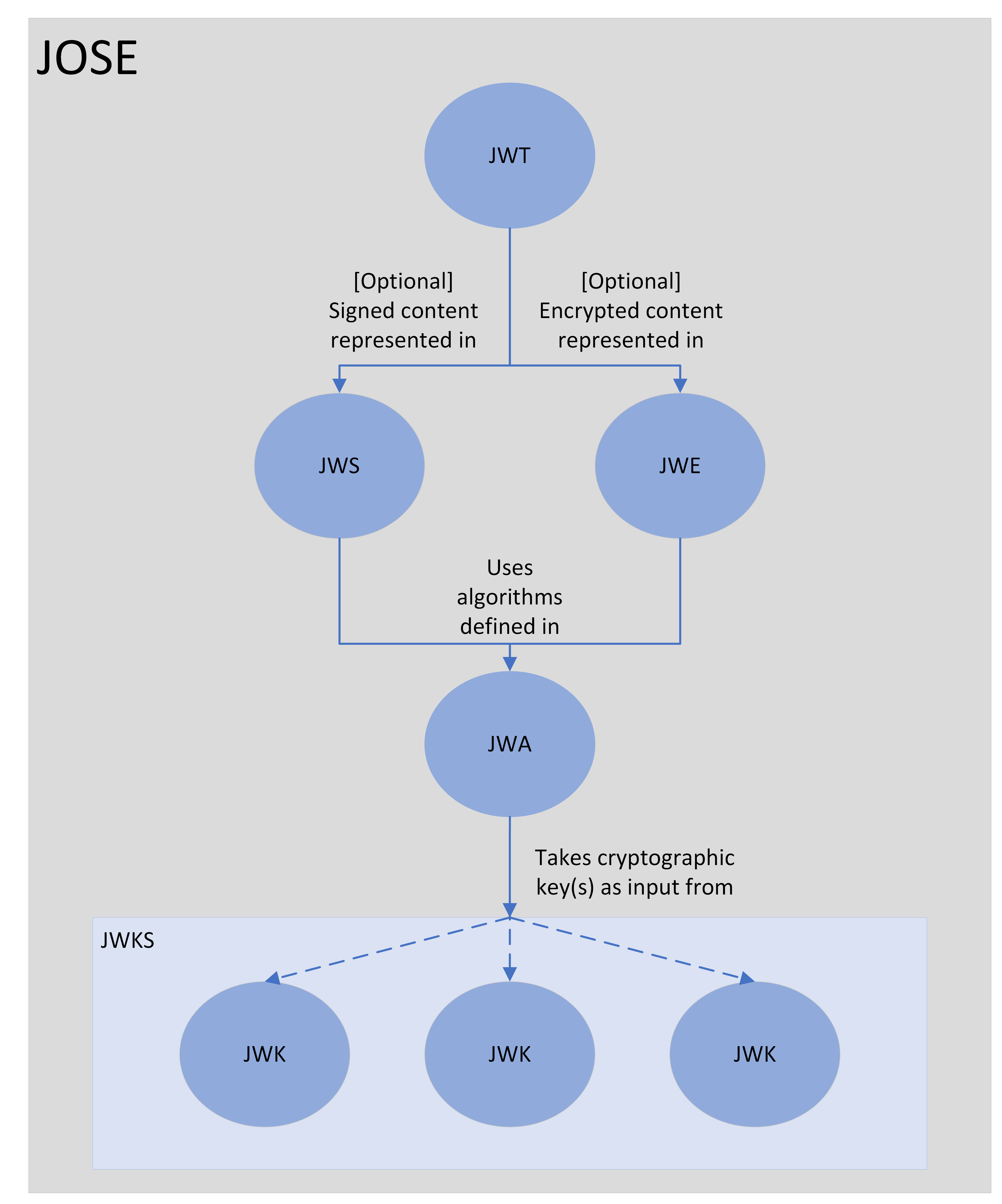
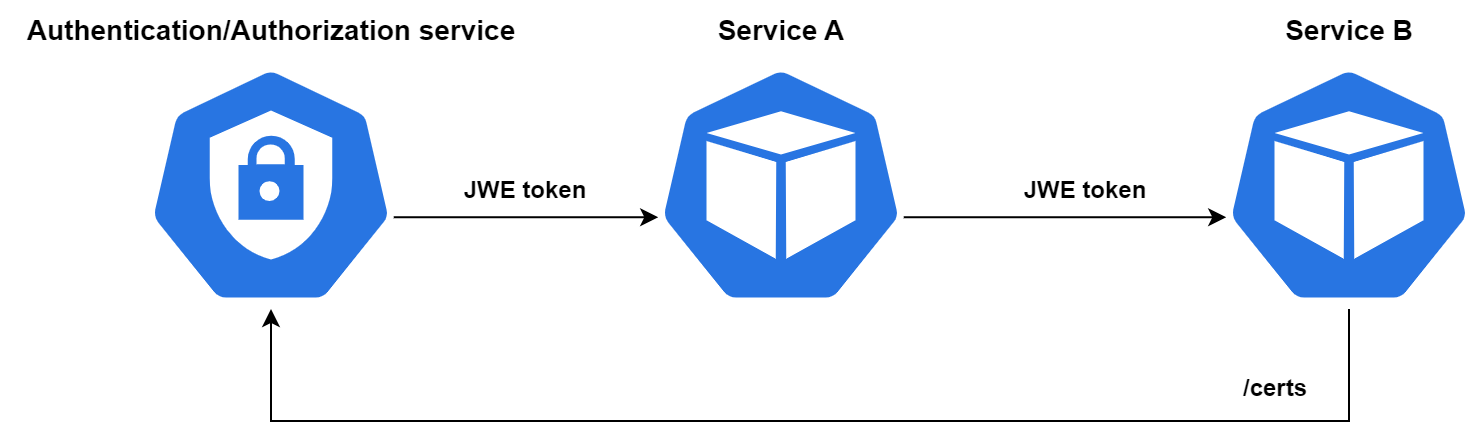
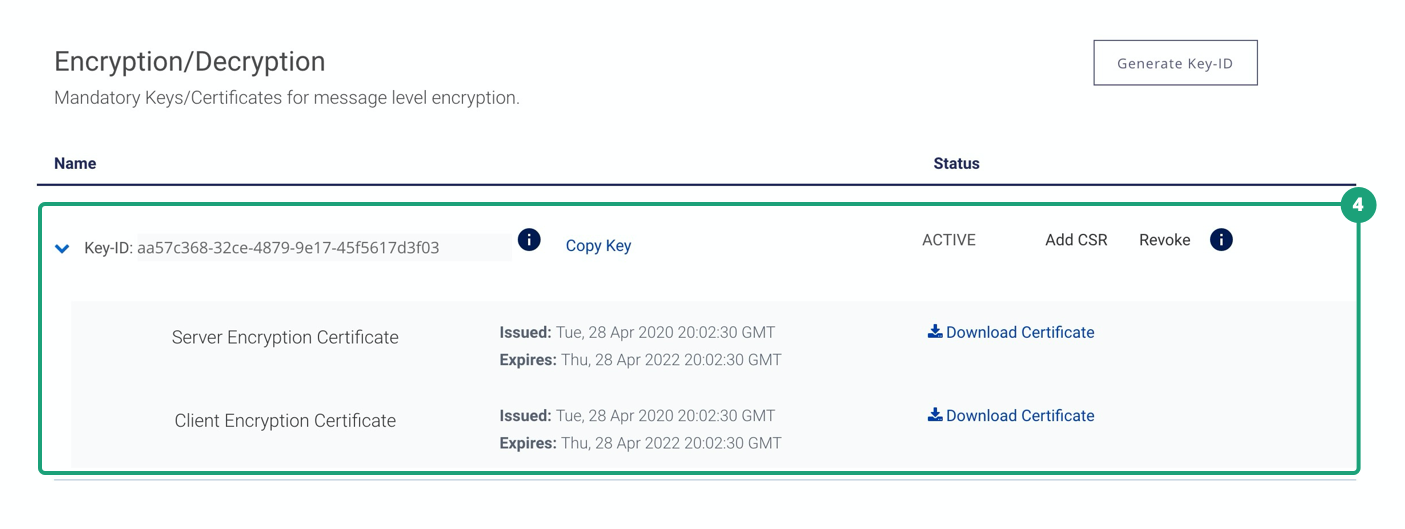
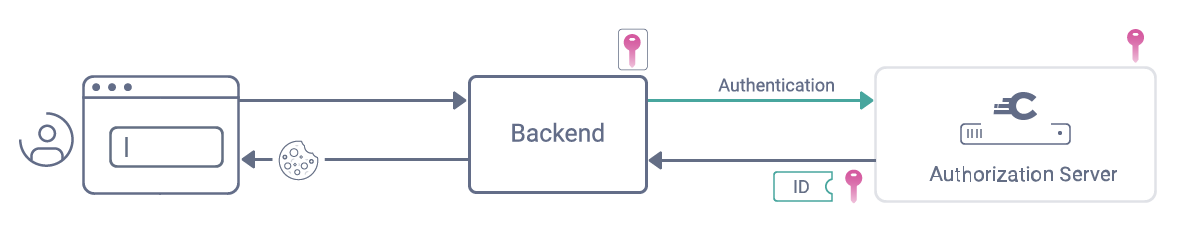
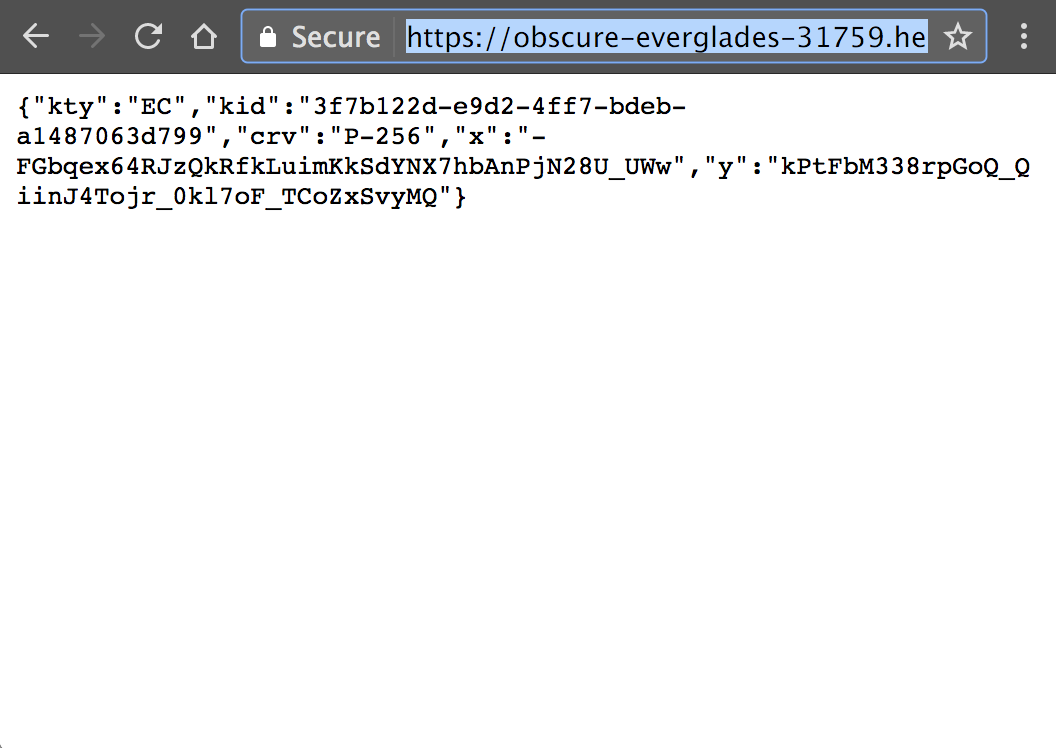
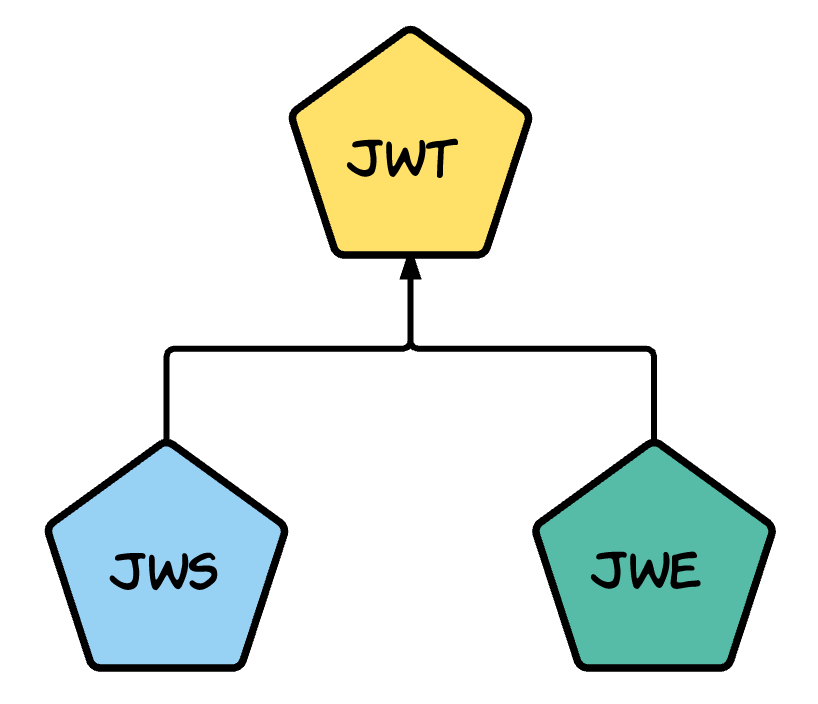
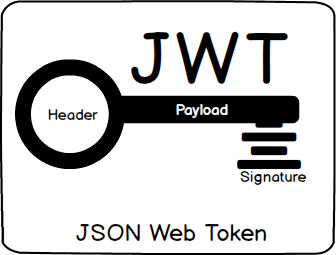
Passing Enduser Attributes to the Backend Using JWE (JSON Web Encryption) WSO2 API Manager 3.2.0 | by Shanaka Sandanayaka | Medium